In the world of networking, the OSI (Open Systems Interconnection) model serves as a conceptual framework that helps us understand how different network protocols and technologies interact with each other. Developed by the International Organization for Standardization (ISO) in the late 1970s, the OSI model has become a fundamental tool for network engineers and IT professionals. In this blog, we will delve into the intricacies of the OSI model, exploring its layers and functions, and gaining a deeper understanding of how data flows through a network.
Contents
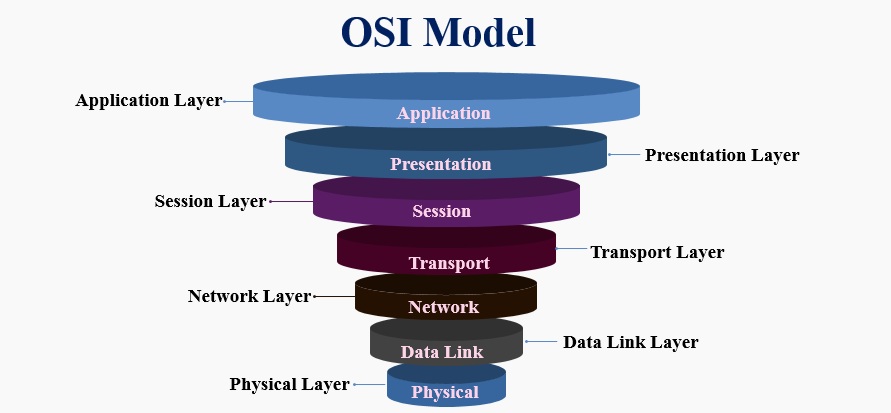
Introduction to the OSI Model

The OSI (Open Systems Interconnection) model is a conceptual framework that standardizes the functions of a communication system into seven distinct layers. It was developed by the International Organization for Standardization (ISO) to facilitate interoperability between different vendors’ networking devices. Each layer in the OSI model has specific responsibilities and communicates with adjacent layers to ensure smooth data transmission across networks.
Layer 1: Physical Layer
The Physical Layer is the first layer of the OSI model. It deals with the physical aspects of communication, such as transmitting raw bits over a physical medium. It defines the electrical, mechanical, and procedural characteristics required to establish and maintain physical connections. Examples of devices operating at this layer include network cables, hubs, and repeaters.
Layer 2: Data Link Layer
The Data Link Layer focuses on providing reliable point-to-point and point-to-multipoint data transfer between adjacent network nodes. It encapsulates data into frames, performs error detection and correction, and controls access to the physical medium. Switches and bridges operate at this layer and use MAC (Media Access Control) addresses for forwarding data.
Layer 3: Network Layer
The Network Layer is responsible for logical addressing, routing, and packet forwarding. It ensures data delivery between different networks by selecting the optimal path based on network conditions and addresses. Routers are the primary devices that operate at this layer. The Internet Protocol (IP) is a crucial protocol used in this layer for addressing and routing data across the Internet.
Layer 4: Transport Layer
The Transport Layer provides end-to-end reliable data transfer services between hosts. It ensures that data is delivered error-free, in the correct order, and without losses or duplications. This layer uses various protocols, such as Transmission Control Protocol (TCP) and User Datagram Protocol (UDP), to establish connections, perform segmentation, and manage flow control.
Layer 5: Session Layer
The Session Layer establishes, manages, and terminates communication sessions between applications. It enables synchronization and checkpointing of data exchange, allowing for efficient error recovery and retransmission. This layer is responsible for establishing dialogues, managing session tokens, and handling session timeouts.
Layer 6: Presentation Layer
The Presentation Layer focuses on data representation, encryption, compression, and protocol conversion. It ensures that data is presented in a format that the application layer can understand. This layer handles tasks like data encryption, character encoding, and compression techniques to enhance efficiency and security during data transmission.
Layer 7: Application Layer
The Application Layer is the topmost layer of the OSI model. It provides a means for end-user applications to access network services. This layer includes protocols like HTTP, SMTP, FTP, and DNS. It enables activities such as file transfer, email communication, web browsing, and domain name resolution.
Benefits of the OSI Model
The OSI model offers several benefits in network design and communication. It provides a clear separation of responsibilities, allowing for modular development and troubleshooting. The layer-by-layer approach simplifies network management and promotes interoperability. It also facilitates the development of standardized protocols and encourages innovation in networking technologies.
Common Protocols in Each Layer

Each layer of the OSI model is associated with specific protocols that perform the necessary functions. Some common protocols in each layer include:
Physical Layer
- Ethernet
- USB
- RS-232
Data Link Layer
- Ethernet (IEEE 802.3)
- Wi-Fi (IEEE 802.11)
- Point-to-Point Protocol (PPP)
Network Layer
- Internet Protocol (IP)
- Internet Control Message Protocol (ICMP)
- Routing Information Protocol (RIP)
Transport Layer
- Transmission Control Protocol (TCP)
- User Datagram Protocol (UDP)
Session Layer
- NetBIOS
- Remote Procedure Call (RPC)
Presentation Layer
- Hypertext Transfer Protocol (HTTP)
- Secure Sockets Layer (SSL)
- Simple Object Access Protocol (SOAP)
Application Layer
- File Transfer Protocol (FTP)
- Simple Mail Transfer Protocol (SMTP)
- Domain Name System (DNS)
Interactions Between Layers
The layers of the OSI model interact with each other to facilitate the transmission of data across networks. Data flows through the layers from the topmost layer (Application Layer) to the bottommost layer (Physical Layer) and vice versa. Each layer adds its header and information to the data, encapsulating it within a specific protocol data unit (PDU).
As data travels from the source to the destination, each layer performs specific tasks. For example, the Application Layer prepares the data for communication, while the Transport Layer segments the data into smaller units and adds sequence numbers. The Network Layer adds logical addresses and determines the best path for data delivery, while the Data Link Layer adds physical addresses (MAC addresses) and performs error detection.
These interactions between layers ensure that data is properly encapsulated, transmitted, and received by the destination device, following a standardized process that allows different network components to work together seamlessly.
OSI Model vs. TCP/IP Model
While the OSI model is widely recognized, another popular networking model is the TCP/IP model. Also, the TCP/IP model is a concise four-layer model that combines several layers of the OSI model. The TCP/IP model includes the following layers:
- Network Interface Layer: Combines the Physical and Data Link Layers of the OSI model.
- Internet Layer: Corresponds to the Network Layer of the OSI model.
- Transport Layer: Equivalent to the Transport Layer of the OSI model.
- Application Layer: Includes aspects of the Session, Presentation, and Application Layers of the OSI model.
The TCP/IP model is widely used in modern networks, especially for internet communication. It is more practical and flexible than the OSI model, making it the de facto standard for networking protocols.
Importance of the OSI Model in Networking

The OSI model is crucial in networking as it provides a standardized framework for understanding and implementing network protocols. It allows different vendors and developers to create compatible networking devices and software by adhering to the same set of principles.
The layer-by-layer structure of the OSI model simplifies network design, troubleshooting, and maintenance. It enables network administrators to isolate and address issues in specific layers without affecting the entire network. The clear division of responsibilities promotes interoperability and allows for the evolution of individual layers without disrupting the entire network infrastructure.
Understanding the OSI model is essential for network professionals, as it provides a common language and reference point when discussing network architectures, protocols, and troubleshooting procedures. It serves as a foundation for learning and working with various networking technologies, ensuring efficient and reliable communication across diverse networks.
Challenges and Limitations of the OSI Model
While the OSI model is a valuable tool in networking, it also has its challenges and limitations. Some of these include:
- Complexity: The OSI model consists of seven layers, each with its own set of protocols and functions. This complexity can make it challenging for beginners to grasp and implement effectively.
- Lack of Flexibility: The rigid layer structure of the OSI model may not always align with the requirements of modern network architectures. As networks evolve, new layers or functionalities may be needed, which the OSI model does not readily accommodate.
- Interoperability Issues: Although the OSI model promotes interoperability, the reality is that different vendors may implement protocols differently or have proprietary protocols that do not align perfectly with the model. This can lead to compatibility issues between different networking devices and software.
- Limited Focus on Real-World Implementations: The OSI model is primarily a conceptual framework and does not provide detailed guidance on real-world network implementations. Network engineers and administrators often need to rely on additional frameworks, best practices, and specific protocols to design and manage networks effectively.
- The dominance of the TCP/IP Model: While the OSI model is widely recognized, the TCP/IP model has become the dominant model in modern networking. As a result, many network professionals primarily focus on understanding and working with the TCP/IP model, potentially overshadowing the OSI model’s relevance.
Conclusion
The OSI model is a fundamental framework that standardizes the functions and interactions of networking protocols. It provides a layered approach to network design, enabling modular development, troubleshooting, and interoperability. Each layer has specific responsibilities, contributing to the successful transmission of data across networks. While the OSI model has challenges and limitations, it remains a vital tool in understanding network architectures and protocols. Network professionals benefit from a solid understanding of the OSI model to design, manage, and troubleshoot networks effectively.
If you are looking to implement any of the Infosec compliance frameworks such as SOC 2 compliance, HIPAA, ISO 27001, and GDPR compliance, Impanix can help. Book a Free consultation call with our experts or email us at [email protected] for inquiries.